PRYVATE SME
Secure Business Messaging With Administrative Control.
Pryvate gives SMEs encrypted messaging, voice and video — governed through a central company control panel.
Replace unmanaged consumer messaging with governed, enterprise-grade communications in days — not months.
Built for regulated industries · Encryption-first architecture · Full governance above the fold

Designed for regulated SMEs in finance, legal, healthcare and advisory environments
HOW IT WORKS
Simple, governed deployment
Company Admin
Sets up Pryvate SME
Controls Users
Approves, manages, revokes
Team Communicates Securely
Encrypted messaging, voice & video
Employees use Pryvate Messenger. Admins govern access and risk through the portal.
OVERVIEW
What you get
Pryvate SME is Pryvate Messenger deployed inside a managed corporate environment—with governance delivered through the SME Management Portal.
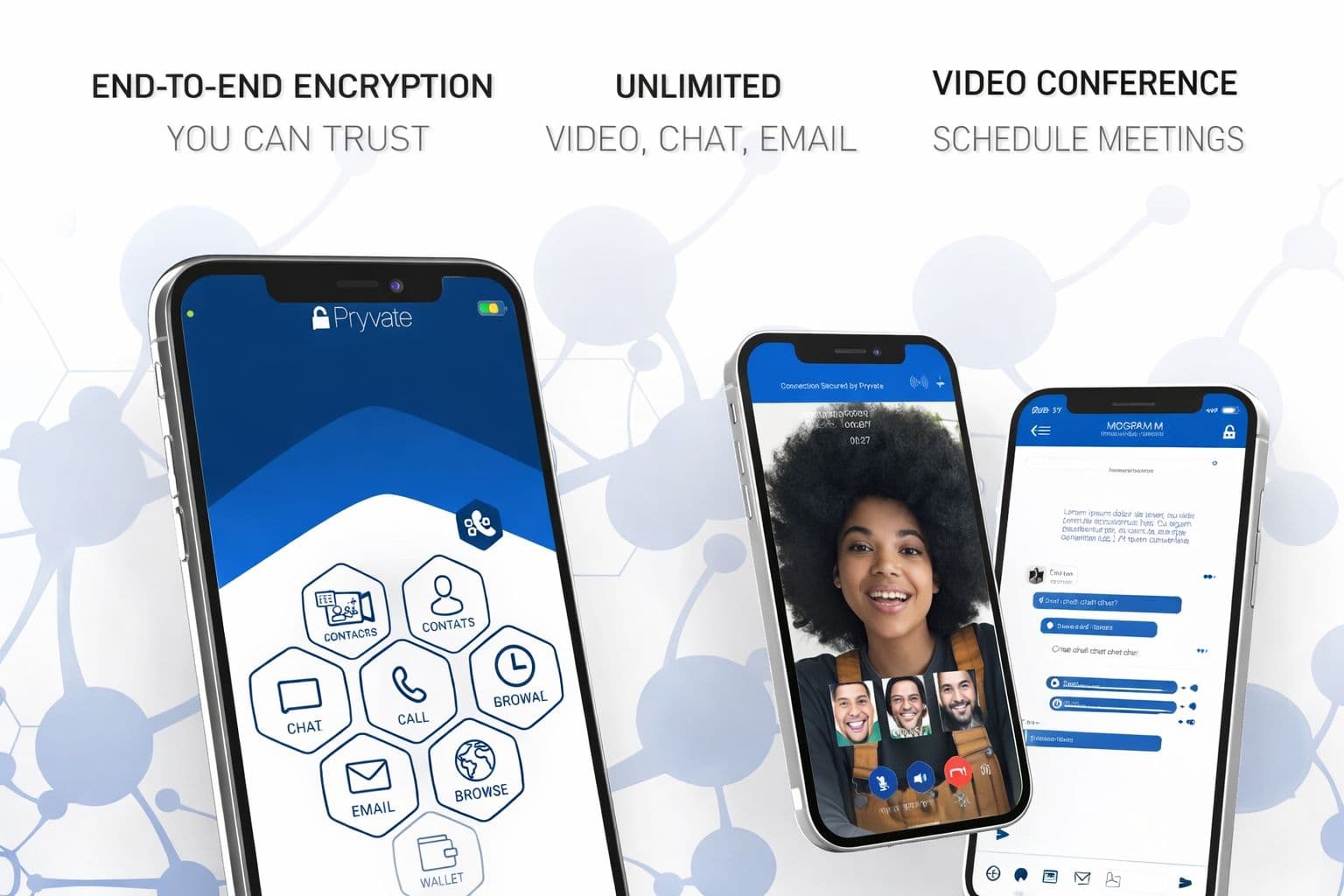
Modern comms
Chat, groups, voice, video, meetings, secure email, file transfer.
End‑to‑end encryption
Encrypted at source. Decrypted only by intended recipients.
Governed access
Approval onboarding, lifecycle states, seat allocation.
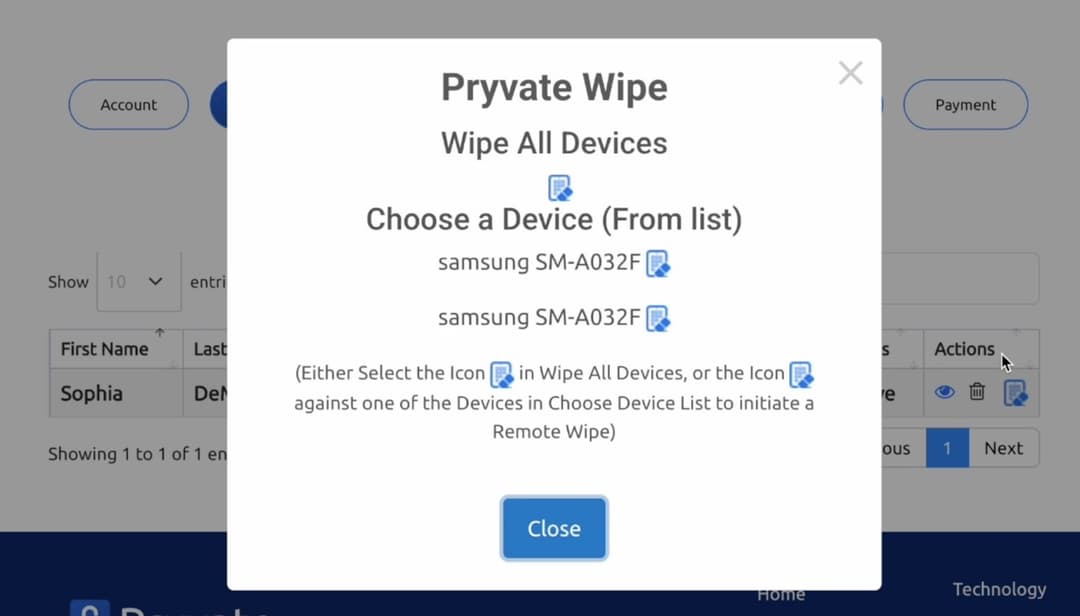
Remote Wipe
Contain risk fast by removing Pryvate data from devices.
THE RISK
The Hidden Business Risk
When employees use consumer messaging apps:
Client conversations leave company control
Ex-employees retain communication history
Lost devices expose business data
Compliance visibility disappears
Businesses cannot remove or govern this data.
With Pryvate, administrators retain control at all times.
WHY SWITCH
Pryvate Was Built For Businesses — Not Users
Consumer platforms assume:
The individual owns communication.
Pryvate assumes:
The organisation governs communication.
That single difference changes risk exposure completely.
Employees already use consumer messaging for business conversations. Pryvate restores governance without changing behaviour.
PORTAL
The control plane for SMEs
The SME Management Portal is what turns encrypted comms into a governed business capability. It gives you measurable controls without enterprise infrastructure.
Approve access
No unmanaged “anyone can join” problem.
Manage lifecycle
Active, suspended, exited—stay on top of who has access.
Contain incidents
Remote Wipe Pryvate data from lost, stolen or exited devices.
Admin actions
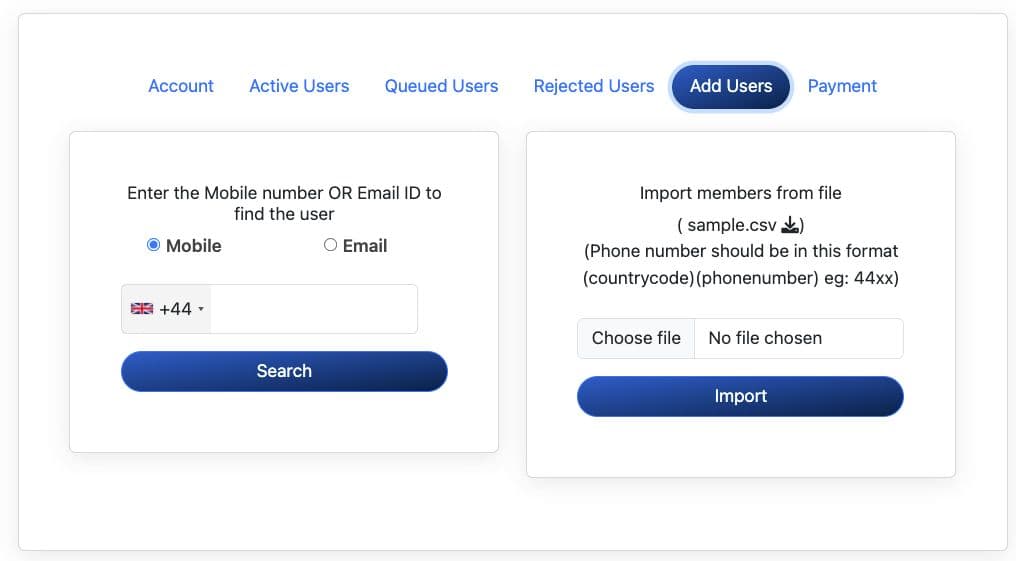
Onboarding
Invite individuals or import via CSV. Approve. Assign seats.
Offboarding
Revoke access immediately. Optionally wipe Pryvate app data.
Seat allocation
Scale your deployment without changing tools.
Portal governs users and devices — without exposing message plaintext.
COMPARISON
How Pryvate Compares
| Capability | Pryvate | WhatsApp Business | Signal | Teams / Slack |
|---|---|---|---|---|
| End-to-End Encryption | Limited context | |||
| Company Ownership of Accounts | Employee-owned | Partial | ||
| Admin User Approval | ||||
| Remote Device Wipe | ||||
| Employee Exit Protection | ||||
| Metadata Minimisation | ||||
| Secure External Communications | ||||
| Built for SME Governance |
Most messaging platforms secure conversations. Pryvate secures organisational control.
INFRASTRUCTURE
The Missing Layer In Modern Business Infrastructure
Businesses today secure:
But communications — where decisions, client data and commercial discussions occur — often remain outside organisational control.
This creates the largest unmanaged risk surface inside most SMEs.
Pryvate Introduces The Secure Communication Layer
Users
Pryvate Secure Communication Layer
Business Governance & Control
- Encrypted messaging, voice and video
- Central administrative governance
- User lifecycle control
- Device‑level risk protection
- Compliance‑aligned communications infrastructure
Instead of managing multiple consumer tools, businesses operate communications through a single governed layer.
ENTERPRISE REALITY
Communication Is Now Business Infrastructure
Every client instruction, commercial decision and internal strategy discussion flows through digital communication.
Yet most organisations still rely on platforms never designed for corporate governance.
Pryvate was built to change that.
Pryvate powers the Secure Communication Layer within modern SME infrastructure.
LIFECYCLE
A rollout your team can operate
Simple, governed, repeatable. Designed for real SME operations—fast onboarding and fast containment.
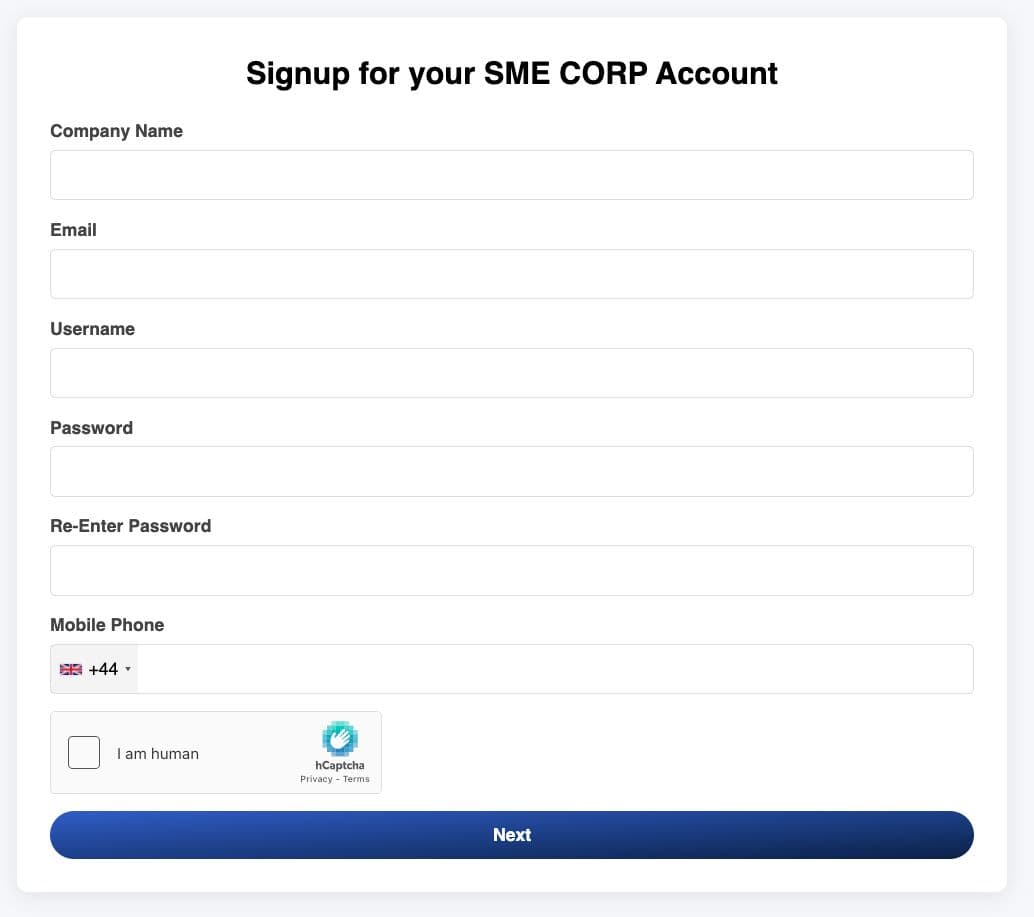
Create environment
Corporate account + portal access. No hardware installation.
Onboard users
Invite/import employees. Approve access.
Operate securely
Chat, calls, meetings, email and files—end‑to‑end encrypted.
Offboard & contain
Revoke access. Remote Wipe Pryvate data when needed.
Remote Wipe is a core risk control
For device loss, theft, employee exit or contract completion, Remote Wipe helps reduce residual data exposure.
Remote Wipe applies to Pryvate application data and does not affect unrelated device data.
SECURITY
Encryption-first by design
Content is encrypted on-device before transmission and decrypted only by intended recipients. Infrastructure routes encrypted traffic and handles signalling — not plaintext content.
Speak to Enterprise Security Team- End‑to‑end encryption with forward secrecy
- Modern elliptic curve key exchange (X25519 / Curve25519 family)
- Ephemeral session keys + rotation to reduce exposure
- Application‑layer encryption for voice/video streams
- No server‑side private key retention (device‑centric key model)
Trust model
Zero‑trust assumption
Transport layers are not trusted with message content.
Only endpoints decrypt
Decryption happens on intended recipient devices.
Control plane ≠ data plane
Admin actions occur without accessing plaintext content.
Metadata minimisation
Limited to routing/reliability—no profiling or monetisation.
PRICING
Simple per‑user pricing
Replace unmanaged messaging with governed encrypted communications from £1 per user — backed by risk reduction and device risk containment.
Pricing subject to contract and volume commitments. Most SMEs justify cost through reduced residual-data risk and faster offboarding.
Speak to Enterprise Security TeamPer-user tiers
| Tier | Price / user |
|---|---|
| Up to 50 users | £2.50 |
| 51–250 users | £2.15 |
| 251–500 users | £1.85 |
| 501–1000 users | £1.40 |
| 1000+ users | £1.00 |
NEXT STEP
See Pryvate SME in action
We’ll review your onboarding/offboarding flow, device risk posture and compliance expectations—then propose a rollout plan.
NDA available. Procurement-safe summaries available on request.
Book a Business Demo
DOWNLOAD
SME governance & security dossier
Risk, workflow, encryption model, governance and pricing—ready for internal review.